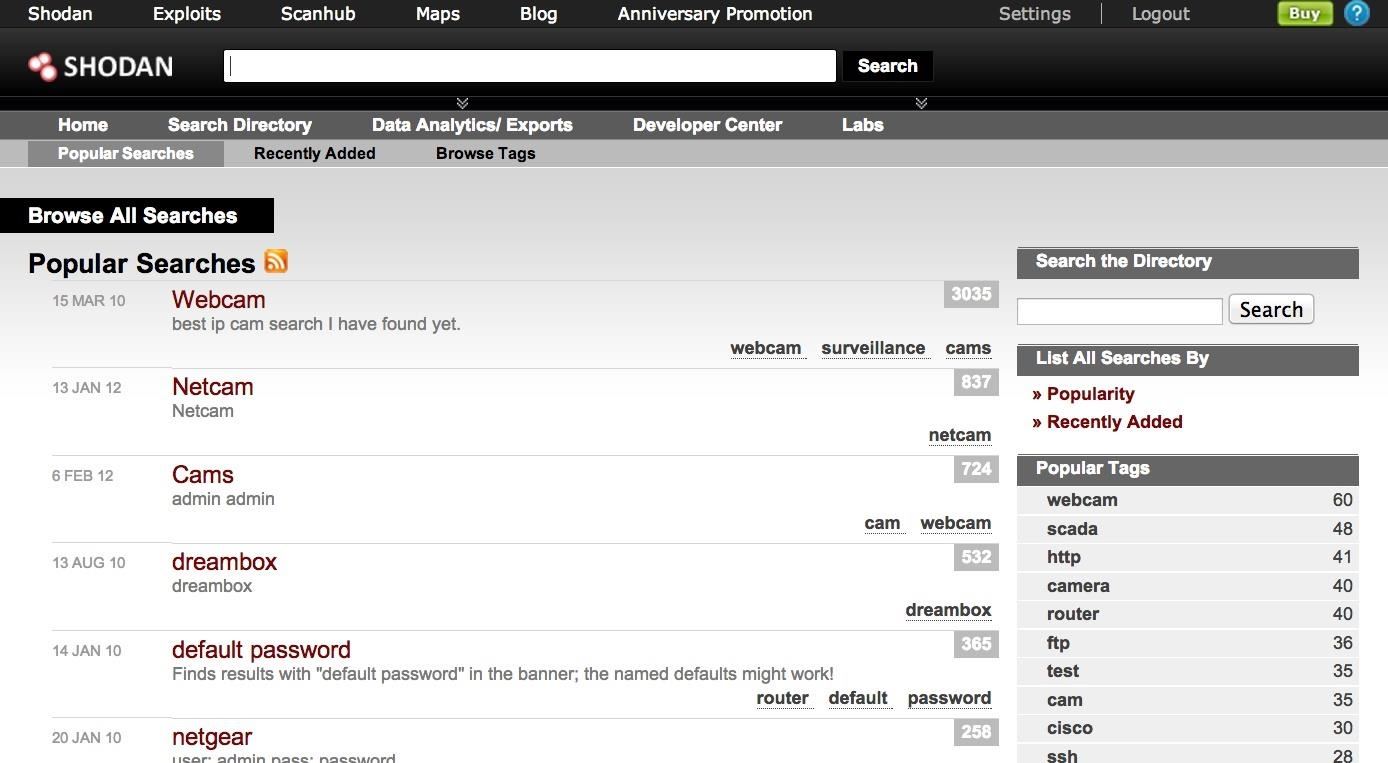
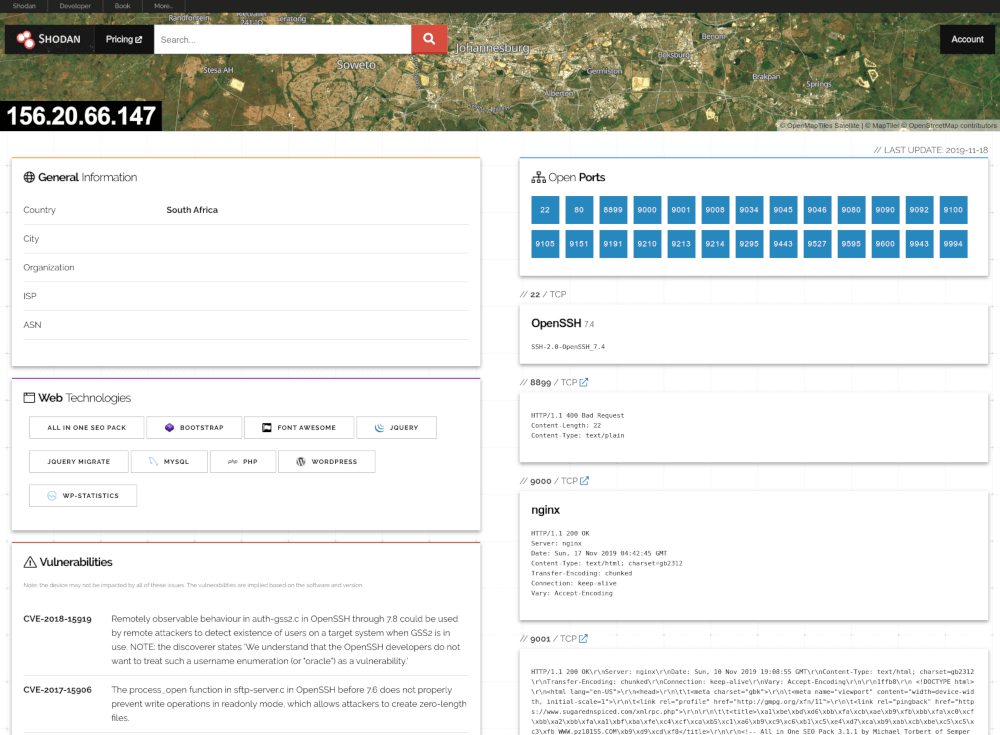
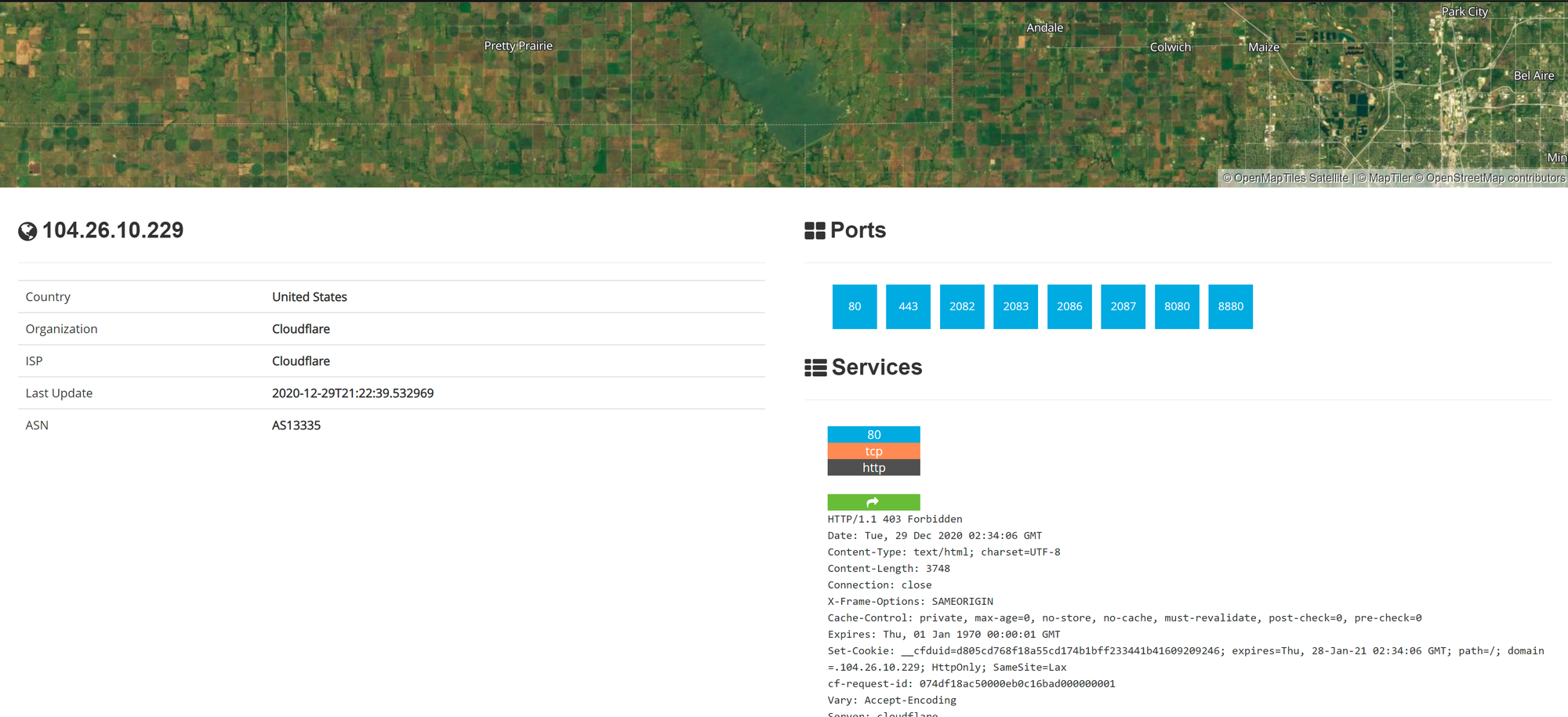
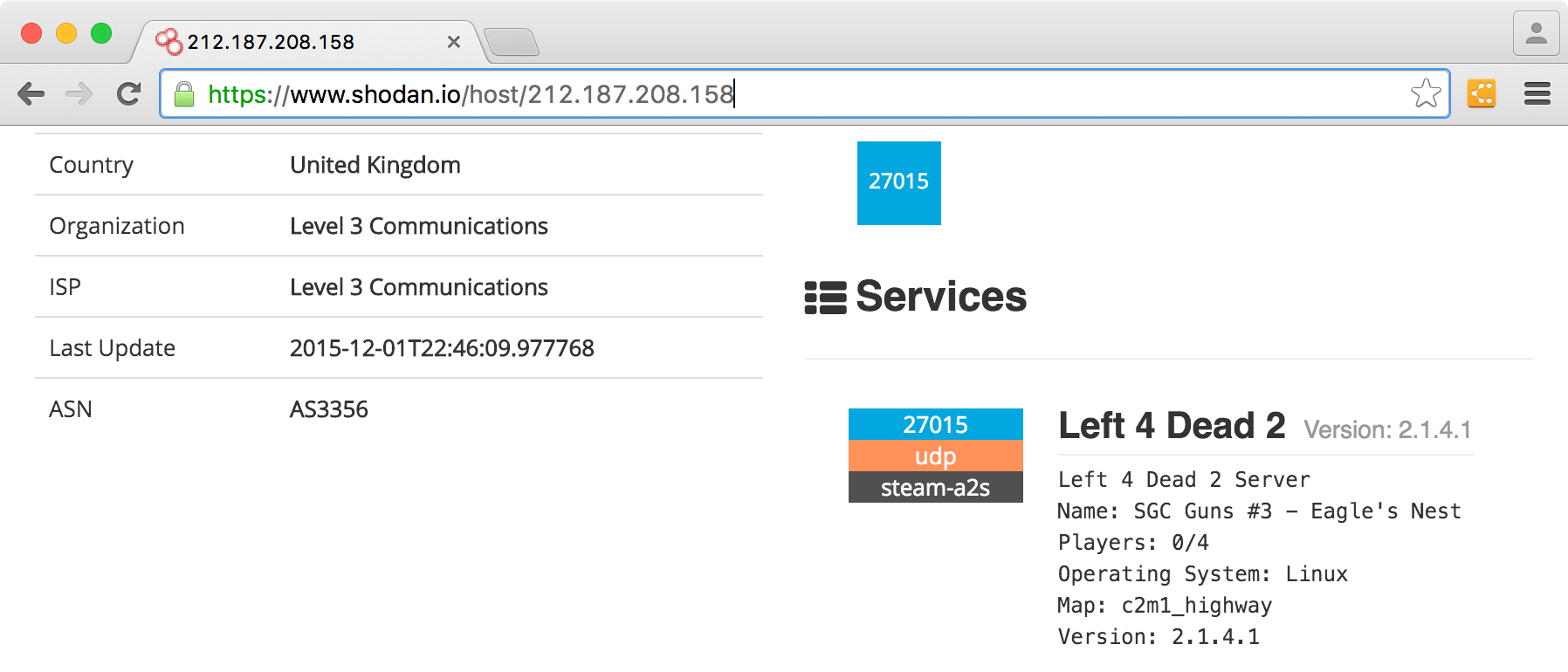
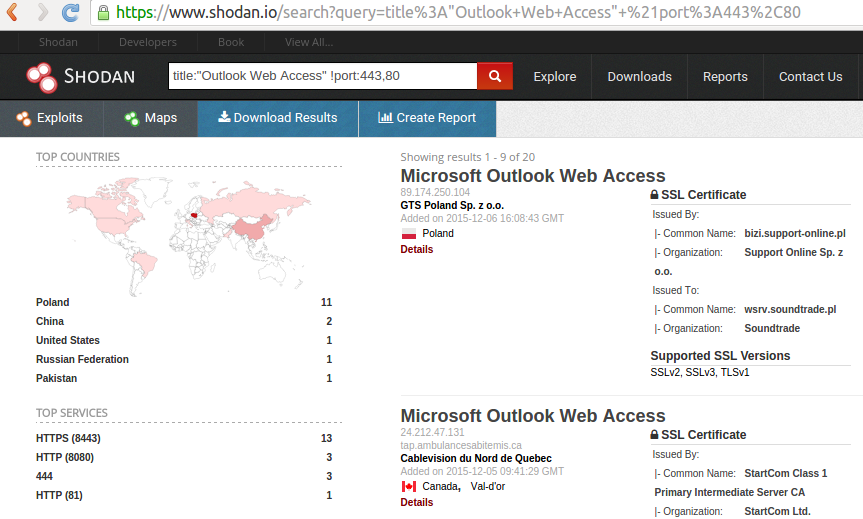
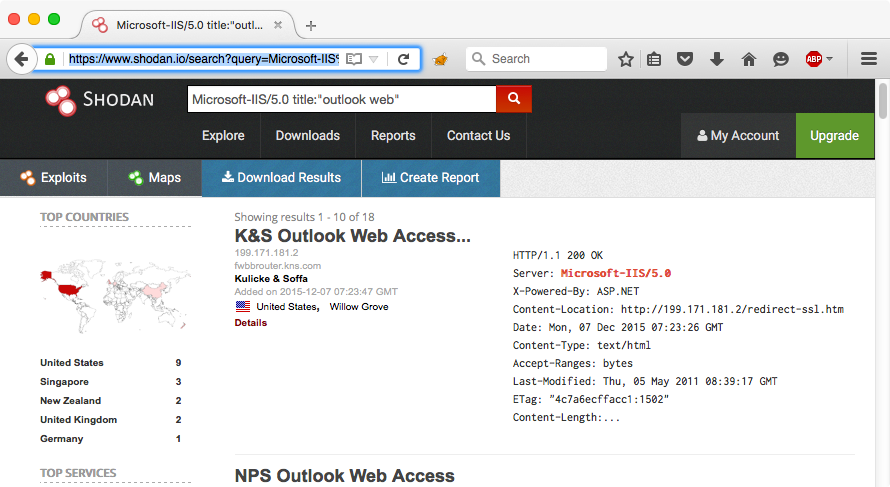
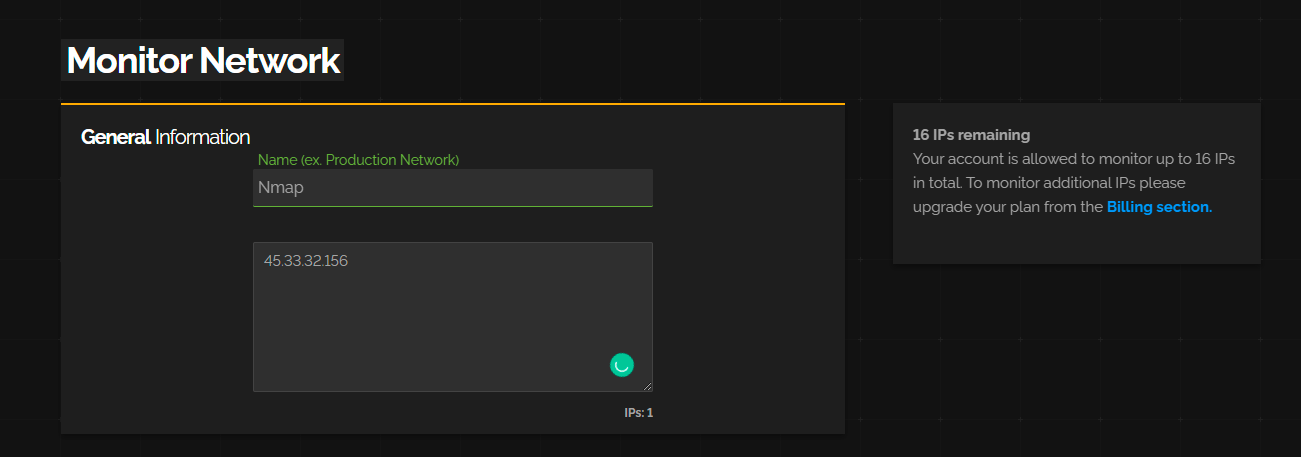
Hack Like a Pro: How to Find Vulnerable Targets Using Shodan—The World's Most Dangerous Search Engine « Null Byte :: WonderHowTo
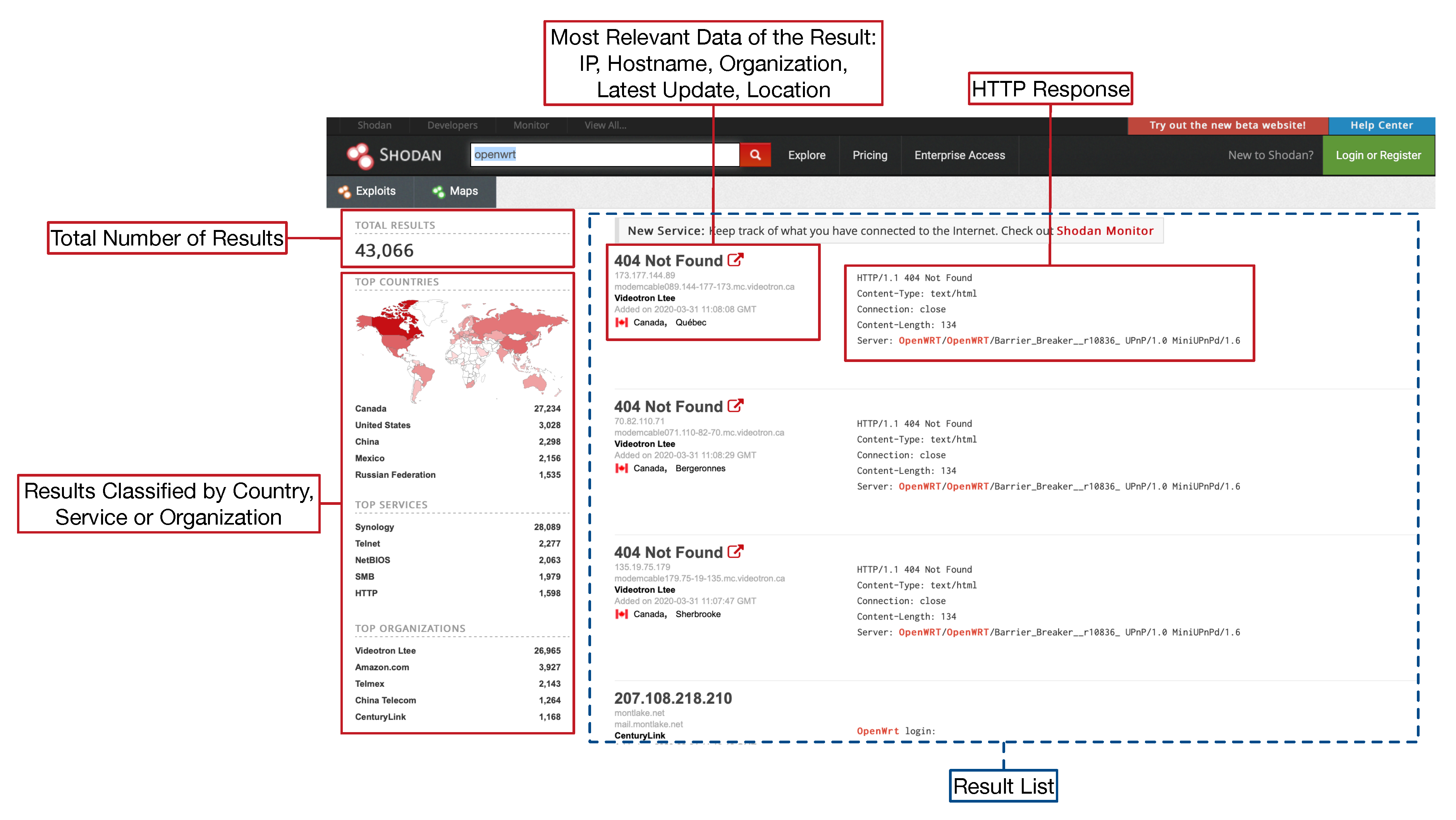
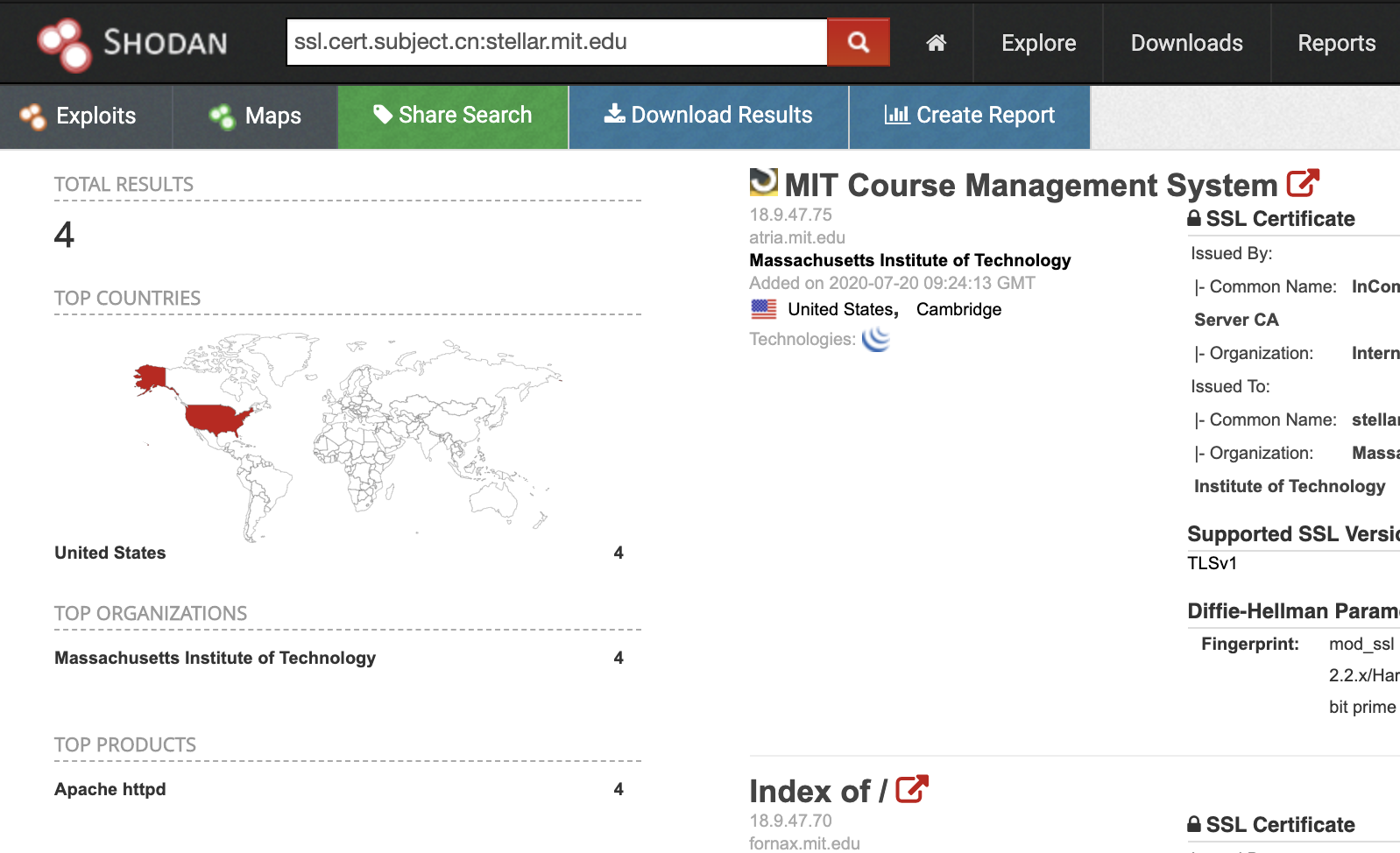
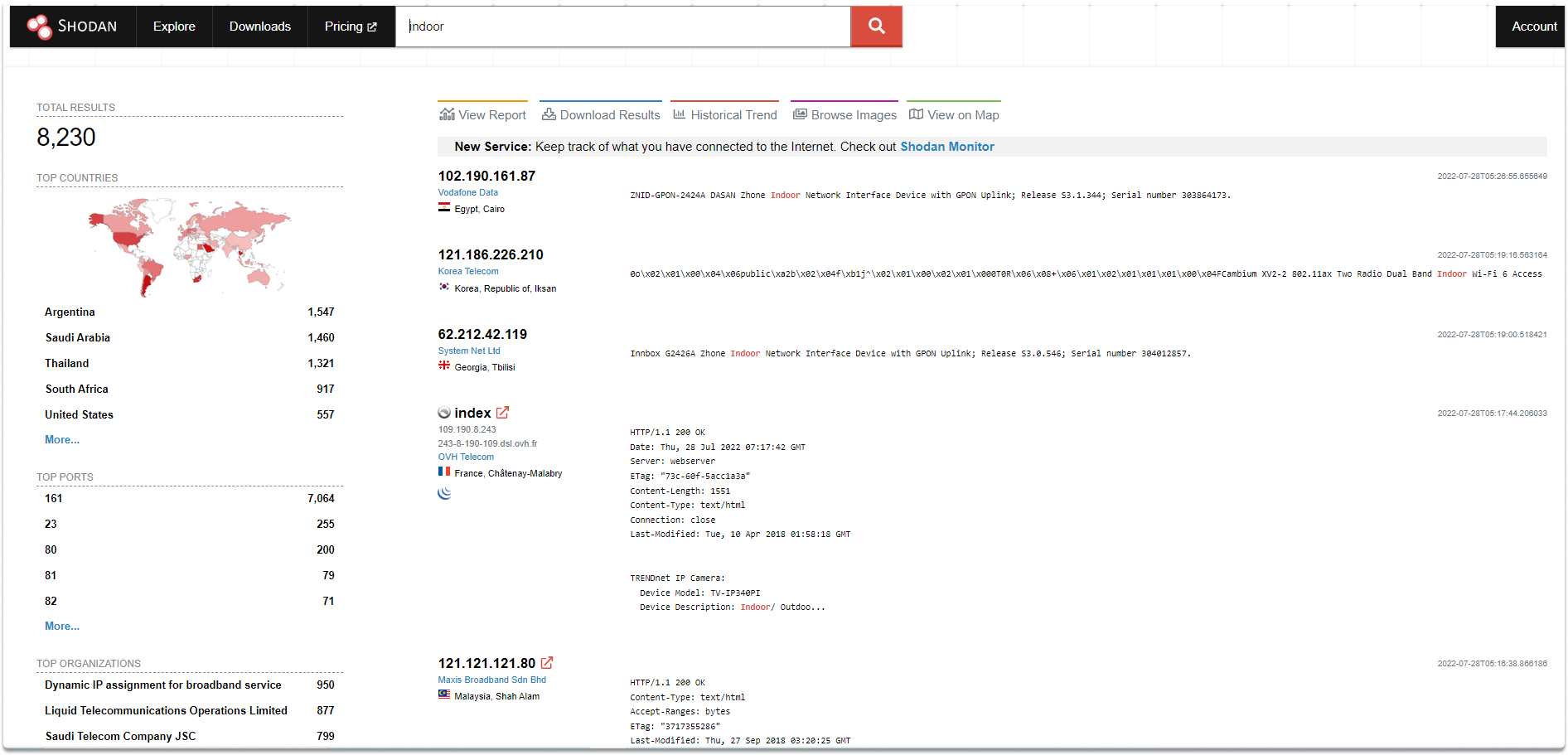
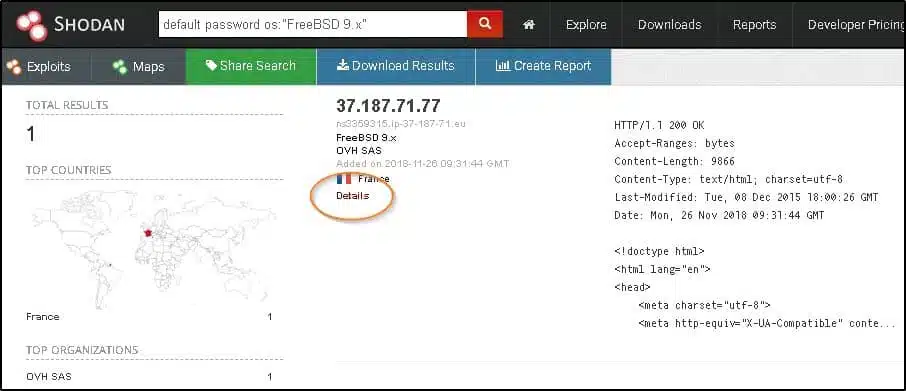
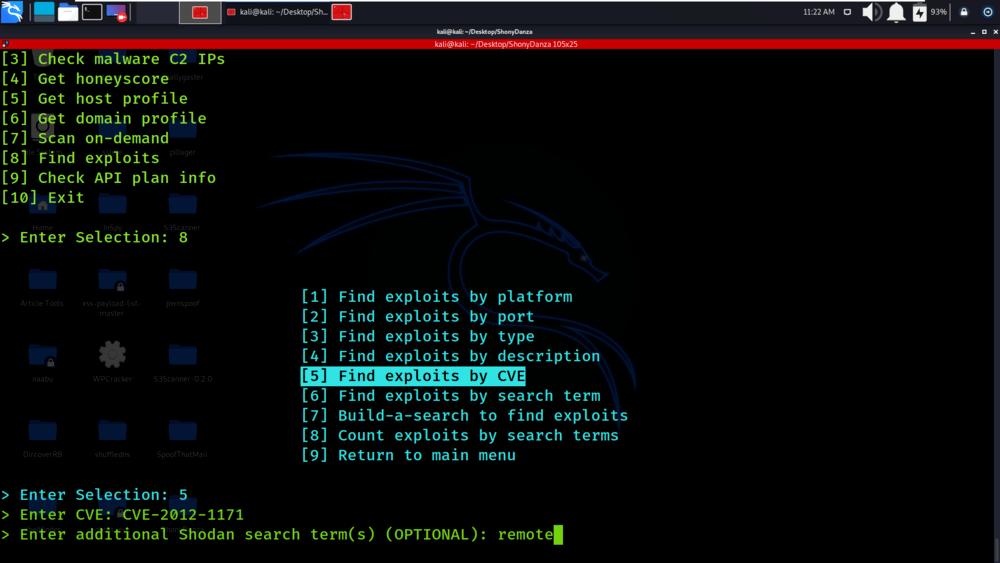
Sensors | Free Full-Text | Teaching and Learning IoT Cybersecurity and Vulnerability Assessment with Shodan through Practical Use Cases


![Search for Vulnerable Devices Around the World with Shodan [Tutorial] Search for Vulnerable Devices Around the World with Shodan [Tutorial]](https://i.ytimg.com/vi/oDkg1zz6xlw/maxresdefault.jpg)